Full Service eCommerce Agency
we assist e-commerce companies in achieving their goals with our magento, shopify, and other e-commerce platform services.
Our services include website development, design, mobile application development, hosting, security, server management, seo, digital marketing, technical audit, conversion optimization, and strategy.
Shopify Services
SEO and Digital Marketing
Server & Security
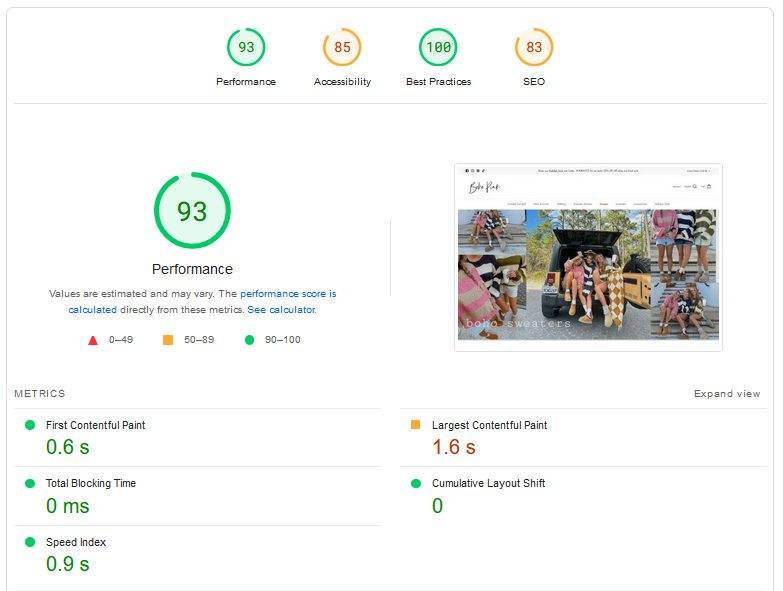
Magento Speed Optimization
Magento Speed Optimization
Having experience of delivering50 plus Magento Speed Optimization projects,
We Guarantee results.
Ecommerce Platforms
We Work With

Enterprises
Offering innovative digitization services for big, medium-sized and small businesses. We deliver state-of – the-art solutions that accelerate innovation for micro, medium-sized and large businesses and help them take a new approach to how they conduct their business in the digital age.

Agencies
Empowering companies, independent software vendors and consulting firms. As their online affiliate, we assist agencies and allow them to successfully manage the programs of their company. We are increasing their existing team or taking full responsibility for their projects
Startups
Enabling start-ups with Internet, Cloud, Mobile and IoT platforms to accelerate their development. We have comprehensive technological expertise and experience to facilitate the start-up growth path at each stage – from the initial Seed phase to the eventual expansion level.
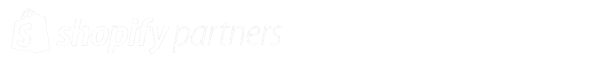
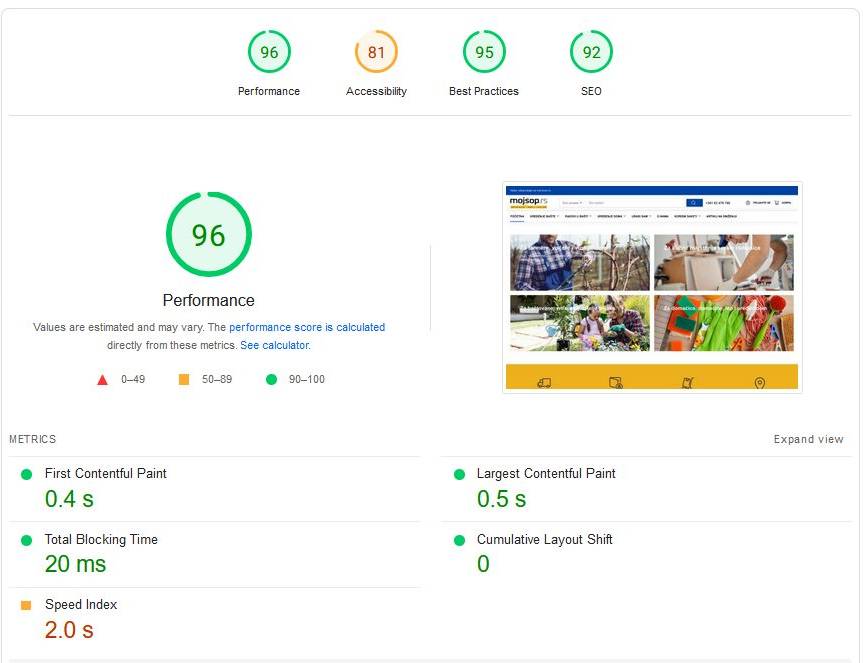
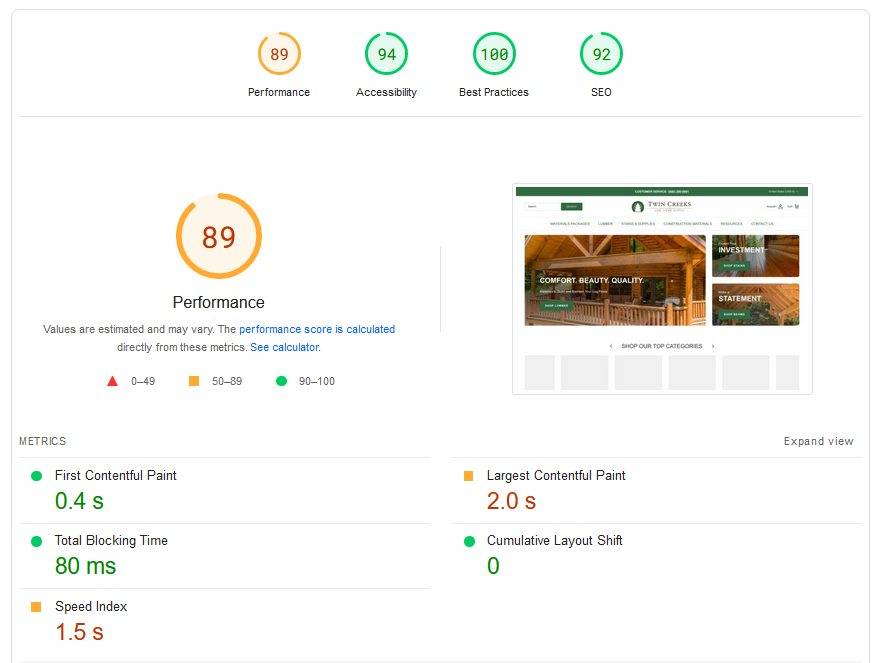
Top Optimized Website Results
Our Strength
500+
Happy Customers
2000
Established In
50+
Skilled Developers
300+
Projects Delivered
Portfolio
Blogs
April 2024
3 Ways Application Performance Monitoring Elevates E-Commerce Success
The Backbone of E-commerce: Accounting Solutions for Online Businesses
Useful Information You Should Know About Mobile Game Development
Leveraging Shopify and SaaS Billing Software to Streamline Sales Processes
Platforms
Testimonials

They always ensure issues are resolved in a timely manner
I had gone through several oscommerce website developers prior to making contact with Satish and his team at OSC Professionals. I always had issues with other companies missing deadlines and not standing up to the bar that was expected when a new project was started. I started working with Satish Mantri in 2009 and have been working on one project after another ever since. From code development for new projects to security and site speed we have accomplished nearly everything we set out to do.

OSC Professionals Pvt Ltd has successfully migrated the platform without downtime, increased site traffic and speed, and improved brand visibility. The team is always available for concerns and responds promptly. Overall, they exhibit a high level of professionalism, timeliness, and communication.
Need to talk about your Project?
We are a full service ecommerce agency and we can help you today!